Credits and sources
Microsoft Learn
https://learn.microsoft.com/en-us/azure/defender-for-cloud/defender-for-key-vault-introductionIntro
In this part of the blog series, I want to show you what Microsoft Defender for Key Vault (MDKV) brings. MDKV helps to protect the Azure Key Vaults against suspicious activities, and it does so without any agent installation. MDKV is one of the most straightforward features to manage. Still, it does protect some of the most sensitive resources you will have in Azure, like, for instance, certificates and secrets used to access your resources and data.
Microsoft Defender for Key Vault features
The features that MDKV offers are protection against:
- Unauthorised access
- Suspicious high volume of requests to key vaults
Microsoft Defender for Key Vault alerts
Microsoft Learn Docs provides a complete list of alerts that MDKV provides; see the link below.
https://learn.microsoft.com/en-us/azure/defender-for-cloud/alerts-reference#alerts-azurekvThe alerts are, for example, “Access from a suspicious IP address to a key vault.”
Managing alerts in the Defender for Cloud uses the alerts view. Like the other Defender services, it is vital to keep your alerting up to date with the correct persons/shared mailboxes to take action on any findings.
How to enable Microsoft Defender for Key Vault
I will enable MDKV on the subscription level.
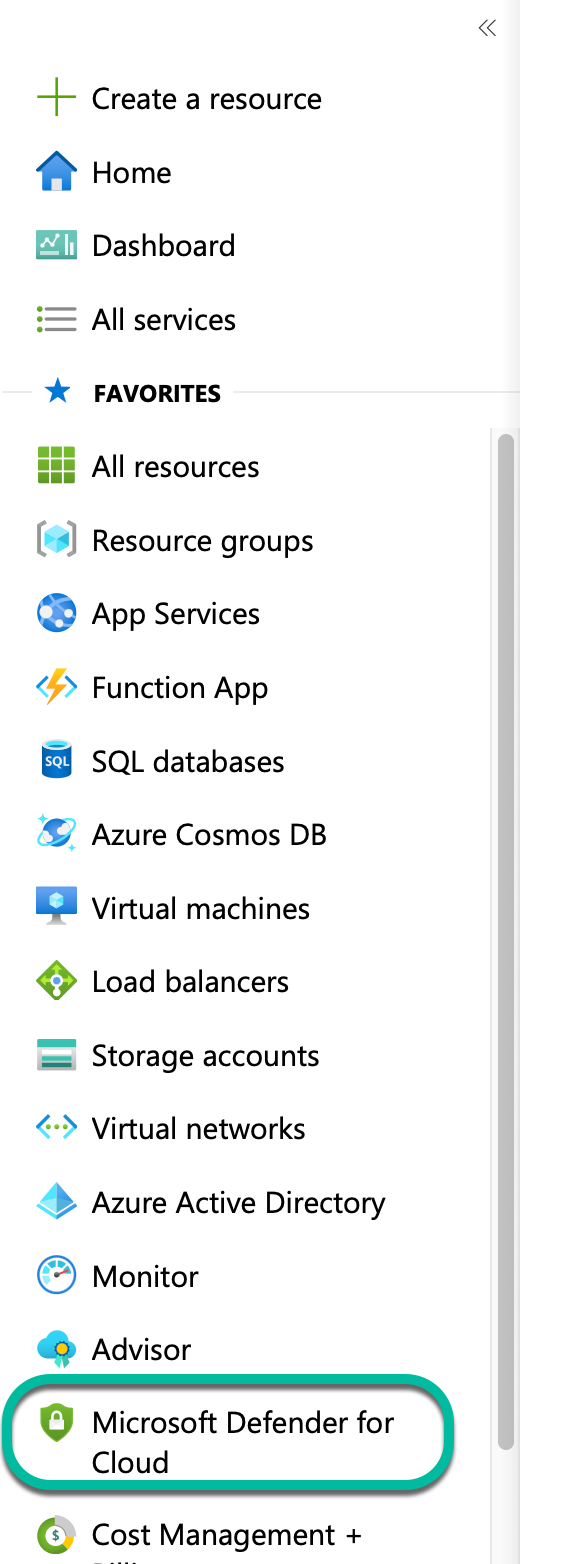
First, go to the Defender for Cloud section in Azure.
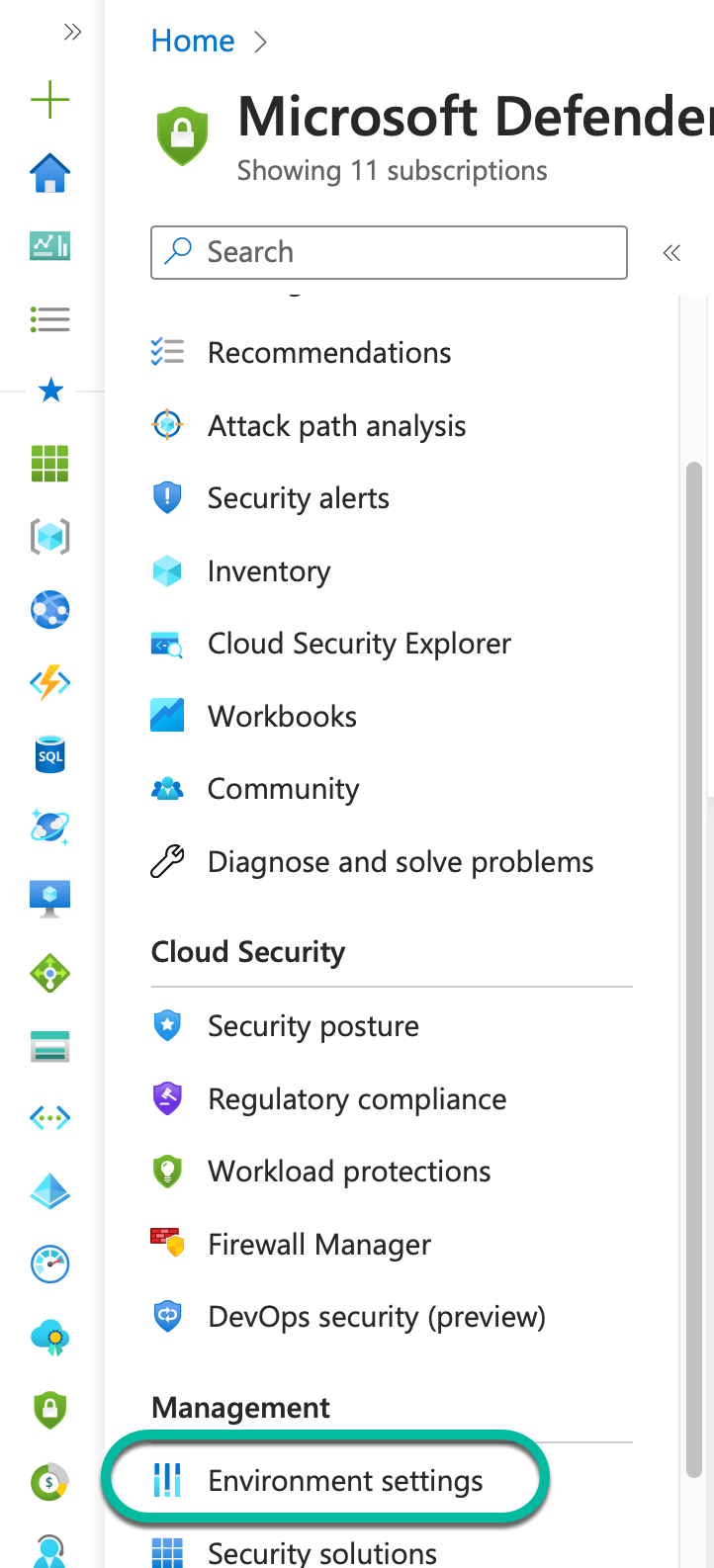
Click “Environment settings.”
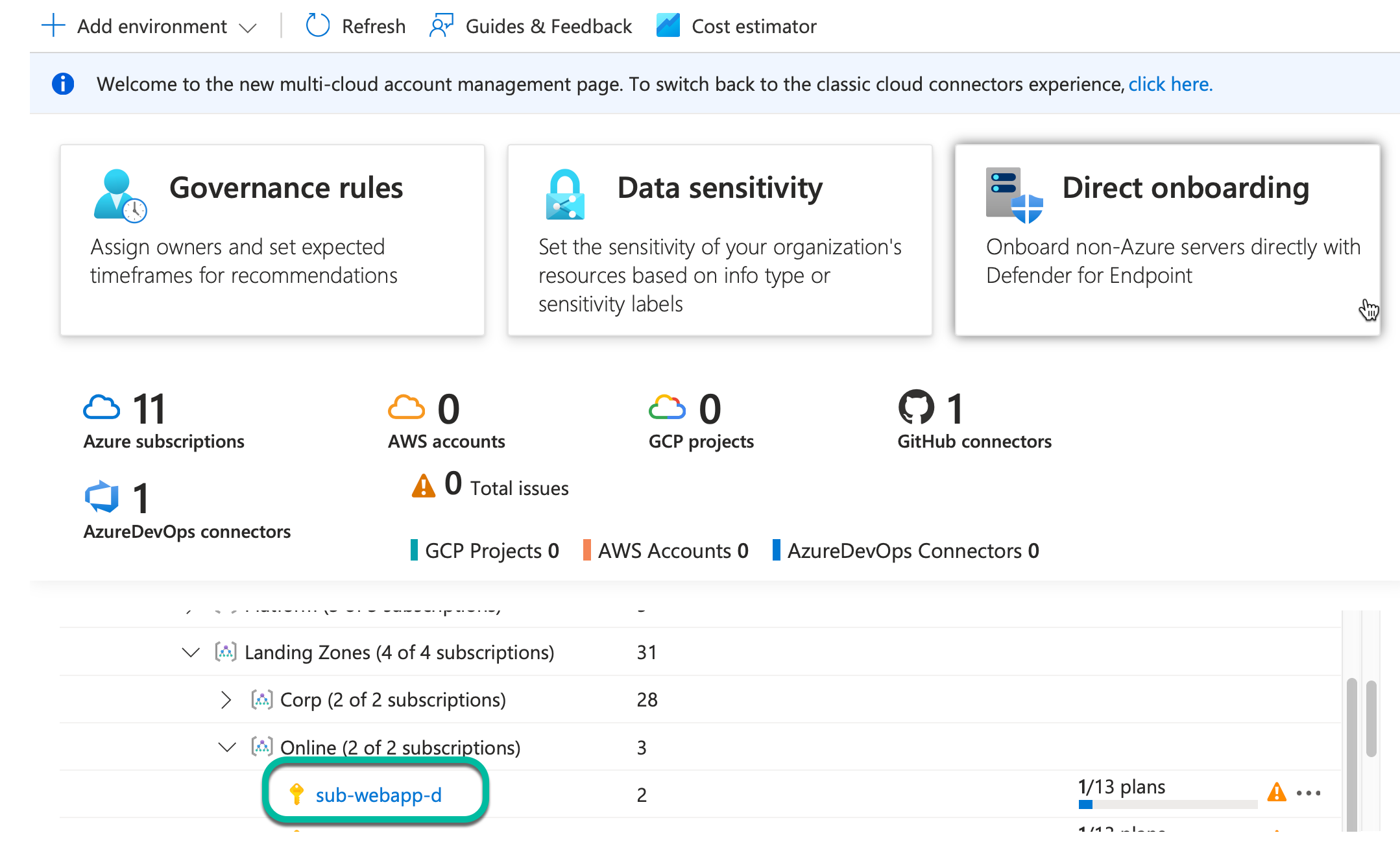
Select the subscription that holds your Key Vault service.
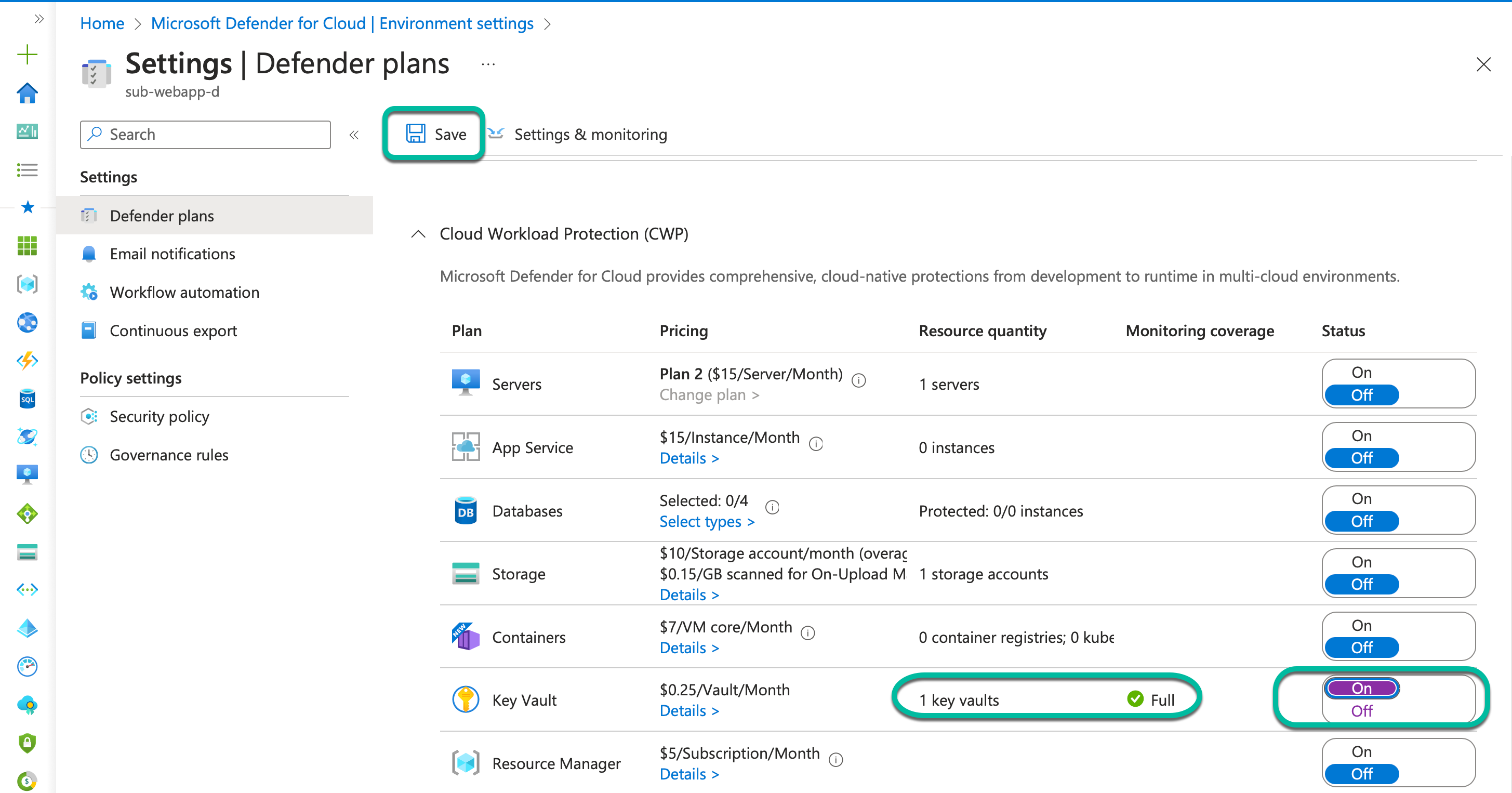
Slide the setting to “On,” and click “Save.”
Conclusion
We now know how to enable Defender for Key Vault, and as you have seen, it is straightforward to enable and use. As we saw with Defender for DNS, there is little to configure for the service. Still, it does provide a security layer on top of secrets and certificates that can contain very sensitive information. I recommend that Defender for key vault should always be considered, and based on the pricing, the protection is often a no-brainer to enable it. If you have key vaults, I encourage you to investigate the pros and cons for your environment and, based on that, decide whether to enable Defender for key vault in your environment.
Join me in the next part of the blog series. This post will be about Defender for servers.